Threat Advisory Report on Petya Ransomware (Critical Severity)
Threat Advisory Report on Petya Ransomware Attack (Critical Severity)
Ransomware: An Introduction
Ransomware is a form of malicious software that locks up users files on the computer system, encrypts them, and demands that the user should pay a specified amount to get the files back.
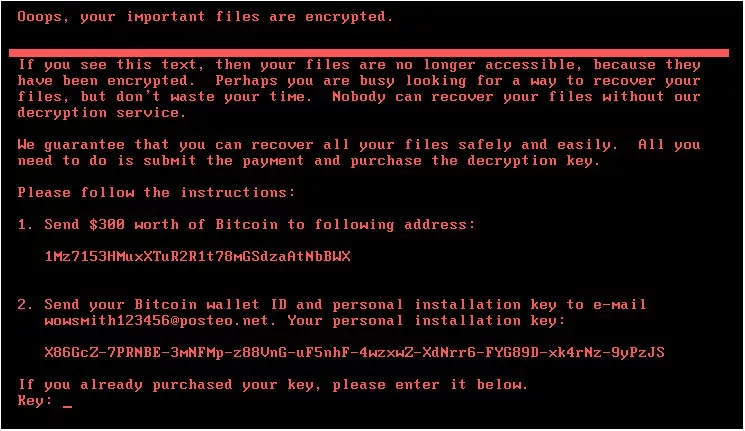
A ransomware that affects Microsoft’s Windows operating system, when a system is infected, a pop up window appears, prompting the user of the system to pay to recover the files within specified time, with a countdown timer. It adds that if the user fails to pay within that time, the fee will be doubled, and if the user doesn’t pay within that period, the user will lose the files forever.
Payment is accepted only in Bitcoins. Experts say that Ransomware is spread by an internet worm- software that spreads copies of itself by hacking into other computers on a network, rather than the usual case of prompting unsuspecting users to open attachments. It is also believed that, the cyber-attack was carried out with the help of tools which were stolen from the National Security Agency (NSA) of the United States.
Petya Ransomware: An Introduction
A new variant of Ransomware known by the name Petya is Spreading like Wildfire.
On June 27, 2017, the world woke up to another ransomware outbreak named as “Petya” also known as “PetWrap” which also uses the same Windows SMBv1 vulnerability that the WannaCry ransomware abused to infect more than 300,000 systems and servers worldwide in just 72 hours in earlier this March.
It uses EternalBlue, CVE-2017-0143 (patched by Microsoft in March) and leverage an additional Shadow Brokers- leaked NSA exploits known as EternalRomance CVE-2017-0145 (patched by Microsoft in March) for remote access as an attack vector and spreading via SMB post-exploitation and uses either PSEXEC or WMIC tools to spread.
Some researchers have also found that, the Ransomware may take advantage of yet another tool published by the ShadowBrokers, known as EsteemAudit, which specifically targets computers running Windows XP and Windows Server 2003.
Note: Microsoft patched those vulnerability as a part of its unprecedented effort to secure its old, unsupported operating systems against leaked NSA exploits.
After further analysis about how Petya infects the MBR (Master Boot Record), Security Researchers found that Petya contains a programming error which destroys some of the MBR, leading to speculation it is a Wiper and intended to destroy data rather than make money by holding it to a ransom, which just trashes the first 24 sector blocks of the disk while replicating itself.
The way the code is set out (i.e. not setting bFinalBlock to True if the file is larger than 1 MB) suggests that, the developer was trying to encrypt files of size 1 MB at a time to avoid using too much RAM, but never got around to writing the code responsible for handling the rest of the file should it exceed 1 MB.
What is a Wiper?
When you erase/delete a file from the computer system, they are not really gone until the areas of the disk it used are overwritten by new information. If the normal Windows delete function is used, the “deleted” file is sent to the Recycle Bin until the space it uses is required by other files.
If Shift+Delete is used to bypass the Recycle Bin, the space occupied by the file is marked as available for other files. However, the file could be recovered days or even weeks later with third-party data recovery software; as long as the operating system does not reuse the space occupied by a file with another file, the “deleted” file can be recovered. While erasing files simply marks file space as available for reuse, data wiping overwrites all data space on a storage device, replacing useful data with garbage data.
So, a Wiper function simply overwrites the deleted files from hard disk with some garbage value and that’s where Wiper function is used.
After further analysis, it is also discovered that the attackers implemented a function that wipes the first 10 sectors of PhysicalDrive0 including the MBR under two conditions:
- If the hash command computed from a running process name (“exe”) returns 0x2E214B44
- If the function that replaces the actual MBR returns an error. Probably as a generic way to detect EDR trying to prevent boot loader modifications.
Is Petya a Ransomware or a Wiper?
The Petya cyber-attack that swept globally, and has infected enterprise networks across Europe is much worse than initially thought. Security researchers have now concluded that, the Petya attack is not a ransomware.
Petya is being termed as a wiper by researchers, with the aim of being mass destruction of user’s data. The idea was never to collect money from victims or enterprises. But it is now used to get ransom from the victims that is why it is called as Ransomware.
Petya has been around since March 2016 and differs from usual ransomware families because it does not encrypt files on a targeted system one by one. Instead, Petya reboots victim’s computers and encrypts the hard drive’s Master File Table (MFT) and renders the Master Boot Record (MBR) inoperable, restricting access to the full system by seizing information about file names, sizes, and location on the physical disk.
Petya replaces the computer’s MBR with its own malicious code that displays the ransom note and leaves computers unable to boot. 2016’s version of Petya was able to modify the disk in a way where it can actually revert its changes, whereas 2017’s version of Petya does permanent and irreversible damage to the disks.
To summarize, it encrypts a system’s MBR in addition to encrypting files. This double stroke renders the disk inaccessible and prevents most users from recovering anything on it.
Petya Ransomware Attack Scenario
The Petya Ransomware infection vector is believed to be the software updater process (EzVit.exe) of a Ukrainian program called MeDoc developed by Ukrainian Company M.E.Doc, and possibly through Microsoft Word documents laced with malicious macros. It combines both a client-side attack (CVE-2017-0199) and a network based threat (MS17-010) to become nastier.
The Current Petya attack is different in the sense that the exploits it uses are only used to spread across a local network rather than the internet. The important difference between WannaCry and Petya is, WannaCry was likely deployed onto a small number of computers and then spread rapidly, whereas Petya seem to have been deployed onto many computers and spreads via local network.
Additionally, using EternalBlue exploit, Petya can also propagate over the network using “WMIC” (Windows Management Instrumentation Command line) by trying credentials gathered from the local machine using “Mimikatz” this allows it to infect network systems which are patched against EternalBlue or not running SMB.
Again, it’s important to note that spreading appears to be limited to only devices on the local network.
Once Petya gets foothold it has two distinct stages. As per the updated information, following is the breakdown for Petya’s two stages:
During the first stage:
- The Windows executable file is dropped and executed.
- Downloads the main binary at hxxp://185.165.29.78/alex/svchost.exe
- This overwrites the beginning of the disk, including the Master Boot Record, and makes an encrypted (XOR) backup of all original data.
- It then clears the windows event log using windows utility Wevtutil
- (wevtutil cl Setup & wevtutil cl System & wevtutil cl Security & wevtutil cl Application & fsutil usn deletejournal /D %c:)
4. It then writes a message to the raw disk partition.
5. At the end, reboot the system at noon as a logic bomb
- (schtasks %ws/Create /SC once /TN “” /TR “%ws” /ST %02d:%02d ; at %02d:%02d %ws) or time specified in parameter defined in DLL component “Rundll32 c:\windows\<dll name>.dll,#1 40”,
- By default, when the malware infects a remote system, it runs the remote DLL with the value “40,” which makes it wait 40 minutes before rebooting the machine.
Note: Stage one ends when the infected device is rebooted.
During the second stage:
- The second stage initiates after the device reboots, and results in the entire drive being encrypted.
- After restarting, a message appears announcing system encryption and asking a Bitcoin $USD300 as a ransom for decrypting the files.
Given this new ransomware’s added lateral movement capabilities, it only takes a single infected machine to affect the entire network. This Ransomware drops a credential dumping tool (typically as a .tmp file in the %Temp% folder) that shares code similarities with “Mimikatz” and comes in 32-bit and 64-bit variants.
Since users frequently log in using accounts with local admin privileges and have active sessions opens across multiple machines, stolen credentials are likely to provide the same level of access the user has on other machines. Once the Ransomware has valid credentials, it scans the local network to establish valid connections on TCP ports 139 & 445.
A special behavior is reserved for Domain Controllers or servers, Petya attempts to call DhcpEnumSubnets() to enumerate DHCP subnets for each subnet, it gathers all hosts/clients (using DhcpEnumSubnetClients()) for scanning for TCP 139 & 445 services. If it gets a response, the malware attempts to copy a binary on the remote machine using regular file-transfer functionalities with the stolen credentials.
It then tries to execute remotely the malware using either PSEXEC or WMIC tools.
It further attempts to drop the legitimate psexec.exe (typically renamed to dllhost.dat) from an embedded resource within the malware. It then scans the local network for admin$ shares, copies itself across the network, and executes the newly copied malware binary remotely using PSEXEC.
In addition to credential dumping, the malware also tries to steal credentials by using the CredEnumerateW function to get all the other user credentials potentially stored on the credential store. If a credential name starts with “TERMSRV/” and the type is set as 1 (generic) it uses that credentials to propagate through the network.
The encryption used by the malware is AES-128 with RSA. This is different from previous variants, which used SALSA20. This ransomware’s encryption behavior depends on the malware process privilege level and the processes found to be running on the machine. It does this by employing a simple XOR-based hashing algorithm on the process names, and checks against the following hash values to use as a behavior exclusion:
- 0x6403527E or 0x651B3005 – if these hashes of process names are found running on the machine, then the ransomware does not do SMB exploitation.
- 0x2E214B44 – if a process with this hashed name is found, the ransomware trashes the first 10 sectors of \\\\.\\PhysicalDrive0, including the MBR
The RSA public key used to encrypt the file encryption keys is hardcoded and can be seen below:
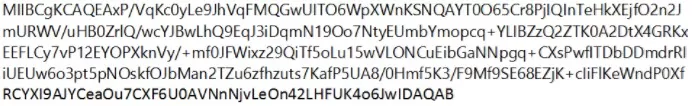
The ransomware attempts to encrypt files that correspond to the following file extensions:
.3ds .7z .accdb .ai .asp .aspx .avhd .back .bak .c .cfg .conf .cpp .cs .ctl.dbf .disk .djvu .doc .docx .dwg .eml .fdb .gz .h .hdd .kdbx .mail .mdb .msg .nrg .ora .ost .ova .ovf .pdf .php .pmf .ppt .pptx .pst .pvi .py .pyc .rar .rtf .sln .sql .tar .vbox .vbs .vcb .vdi .vfd .vmc .vmdk .vmsd .vmx .vsdx .vsv .work .xls .xlsx .xvd .zip
Following Hashes are generated by Petya which can help detecting it;
- 027cc450ef5f8c5f653329641ec1fed91f694e0d229928963b30f6b0d7d3a745 (main 32-bit DLL)
- 64b0b58a2c030c77fdb2b537b2fcc4af432bc55ffb36599a31d418c7c69e94b1 (main 32-bit DLL)
- f8dbabdfa03068130c277ce49c60e35c029ff29d9e3c74c362521f3fb02670d5 (signed PSEXEC.EXE)
- 02ef73bd2458627ed7b397ec26ee2de2e92c71a0e7588f78734761d8edbdcd9f (64-bit EXE)
- eae9771e2eeb7ea3c6059485da39e77b8c0c369232f01334954fbac1c186c998 (32-bit EXE)
Petya uses following files for infecting the systems;
- c:\windows\dllhost.dat
- c:\windows\<malware_dll> (no extension)
- %TEMP%\<random name>.tmp (EXE drop)
In environments where command-line logging is available, the following command lines may be searched:
- Scheduled Reboot Task: Petya schedules a reboot for a random time between 10 and 60 minutes from the current time
- schtasks /Create /SC once /TN “” /TR “<system folder>\shutdown.exe /r /f” /ST <time>
- cmd.exe /c schtasks /RU “SYSTEM” /Create /SC once /TN “” /TR “C:\Windows\system32\shutdown.exe /r /f” /ST <time>
This may be surfaced by searching for EventId 106 (General Task Registration) which captures tasks registered with the Task Scheduler service.
Lateral Movement (Remote WMI)
- “process call create \”C:\\Windows\\System32\\rundll32.exe \\\”C:\\Windows\\perfc.dat\\\” #1”
Network indicators in environments where NetFlow data are available, this ransomware’s subnet-scanning behavior may be observed by looking for the following:
- Workstations scanning ports tcp/139 and tcp/445 on their own local (/24) network scope
- Servers (in particular, domain controllers) scanning ports tcp/139 and tcp/445 across multiple /24 scopes
Following Domains are believed to be infected with Petya:
- hxxp://petya3jxfp2f7g3i.onion/
- hxxp://petya3sen7dyko2n.onion/
- hxxp://mischa5xyix2mrhd.onion/MZ2MMJ
- hxxp://mischapuk6hyrn72.onion/MZ2MMJ
- hxxp://petya3jxfp2f7g3i.onion/MZ2MMJ
- hxxp://petya3sen7dyko2n.onion/MZ2MMJ
- hxxp://mischapuk6hyrn72.onion/
- hxxp://benkow.cc/71b6a493388e7d0b40c83ce903bc6b04.bin COFFEINOFFICE.XYZ
- hxxp://french-cooking.com/
Countries that reported Petya infections include, but are not limited to, Russia, Ukraine, Spain, France, United Kingdom, the United States and India. The Extortion for Petya infections are set at $300 in bitcoins per infected device.
Reported affected industries include, but are not limited to: financial services; retail, hospitality and travel; and energy and utilities.
Researchers also believed that the attacker took an existing Ransomware which he repackaged and resulted in chaos.
- Attack PoC

- Advisory Notes
The EternalBlue SMB vulnerability was originally published by the Shadow Brokers who allegedly acquired NSA hacking tools. The vulnerability was published in April 2017 but patched prior to release by Microsoft in March 2017. The exploit is particularly dangerous because Petya Ransomware uses remote code execution vulnerability that does not require any user interaction.
Since the ransomware propagates primarily through the exploitation of the EternalBlue SMB vulnerability, multiple infections in the same organization are to be expected. This is because the exploit leverages a previously-patched Windows vulnerability and uses either PSEXEC or WMIC tools along with other lateral spreading techniques like stealing admin credentials to spread across a local network rather than the internet as mentioned earlier.
Researchers have also suggested not to pay any ransom as the email address “wowsmth123456[at]posteo[dot]net” which the Petya Ransomware asks you to contact upon payment has been blocked by the email provider, “Posteo” so making payment confirmation is pretty much impossible.
Early analysis indicates that for the current variant of Petya, administrators can stop the spread within a network from the Windows Management Instrumentation by blocking the file “C:\Windows\perfc.dat” from running.
Administrators can also shore up their defenses by using Microsoft’s Local Administrator Password Solution to protect credentials that grant network privileges. Researchers also found that the Petya runs on boot, meaning that if system is disrupted before Windows boots, or by quickly powering down once screen displays a fake “Check Disk” message, files encryption can be avoided.
If MS17-010 is not patched, the malware will spread via Microsoft Server Message Block. If MS17-010 is patched and the malware has admin rights, it will spread laterally via either PSEXEC or WMIC as mentioned in earlier sections.
Note: The actor(s) behind this activity is currently unknown and no major group has taken credit for the activity.
Mitigation Techniques for Petya Ransomware
To safeguard the organization from Petya outbreak, Varutra Consulting recommends the following:
- Prevent reboot after blue screen, thereby preventing stage 2 encryption.
- Microsoft patches- MS17-010, SMB Server patches need to be applied over the network.
- Disable SMB v1 and block all versions of SMB by blocking TCP port 445 with related protocols on UDP ports 137-138 and TCP port 139 at network perimeter.
- Ensure Microsoft Knowledge Base KB4015546 & KB4015549 has been applied to all the systems as Petya leverages CVE-2017-0199.
- As the Email used for the Petya Ransomware is “wowsmth123456[at]posteo[dot]net” detect/blacklist all incoming emails from wowsmth123456[at]posteo[dot]net at network boundary.
- Below mentioned are the possibly infected IP’s which need to be blocked on firewall immediately “95.141.115[dot]108”, “185.165.29[dot]78”, “84.200.16[dot]242”, and “111.90.139[dot]247”
- Do not pay any ransom associated with this activity. The actors may not even provide a decryption key, and furthermore doing so incentivizes and finances further criminal activity.
- Enable strong Spam filters to prevent phishing e-mails from reaching the end users and authenticate in-bound e-mail using technologies like Sender Policy Framework (SPF), Domain Message Authentication Reporting and Conformance (DMARC) and Domain Keys Identified Mail (DKIM) to prevent e-mail spoofing.
- Disable macro scripts from Microsoft Office files transmitted via e-mail.
- Implement Endpoint Controls to Protect the Windows AppData Folder.
- Prevent privileged execution of windows binaries from temp directories.
- User education should involve frequently advising users of how attackers are trying to gain a foothold in the environment.
- Advising users not to open Email attachments unless they are expecting it. Only open Email attachments received from trusted source.
- If a document from an email is opened in Protected Mode, a user should not enable editing of the document unless they expected the document and know who sent it.
Read about WannaCry Ransomware Threat Advisory blog post here
References:
- https://securingtomorrow.mcafee.com/mcafee-labs/new-variant-petya-ransomware-spreading-like-wildfire
- http://seckurity.com/2017/06/everything-technical-about-the-new-ransomware-petya
- https://www.optiv.com/blog/intelligence-advisory-new-petya-ransomware-outbreak
- https://www.malwaretech.com/2017/06/petya-ransomware-attack-whats-known.html
- https://blogs.technet.microsoft.com/mmpc/2017/06/27/new-ransomware-old-techniques-petya-adds-worm-capabilities/
- https://www.wired.com/story/petya-ransomware-wannacry-mistakes/
- https://securelist.com/expetrpetyanotpetya-is-a-wiper-not-ransomware/78902/
Authors:
Lekhraj Rawat and Umang Waghmare