Threat Advisory Report on WannaCry Ransomware (Critical Severity)
Here we will discuss Threat Advisory Report on WannaCry Ransomware (Critical Severity).
1. Introduction
On Friday, May 12, countless organizations around the world began fending off attacks from a ransomware strain variously known as WannaCrypt, WanaDecrypt and Wanna.Cry.
Security researchers found “WannaCry” or “WannaDecryptor”; a type of ransomware which spreads from system to system silently and remains invisible to users until it unveils itself and then warns users that all their files have been encrypted with a key known only to the attacker and that they will be locked out until they pay to an anonymous party using the cryptocurrency Bitcoin.
Ransomware encrypts a victim’s documents, images, music and other files unless the victim pays for a key to unlock them.
Wana Decrypt0r triggered security alerts for ETERNALBLUE, an alleged NSA exploit. ETERNALBLUE works by exploiting a vulnerability in the SMBv1 protocol to get a foothold on vulnerable machines connected online. Microsoft patched the flaw in MS17-010, released in March, but there are high chances that all Windows PC owners have applied the security update.
On Friday, at least 16 hospitals in the United Kingdom were forced to divert emergency patients after computer systems there were infected with Wanna. According to multiple stories in the British media, approximately 90 percent of care facilities in the U.K.’s National Health Service are still using Windows XP – a 16-year-old operating system.
2. Attack Scenario
The initial infection vector of WannaCrypt 2.0 is not confirmed. It is possible that the initial vector is spam with malicious attachments (.pdf, .hta, and macro embedded MS Office files) commonly used in other ransomware campaigns.
Once WannaCry 2.0 achieves a foothold, the ransomware infects other machines by leveraging a remote command execution vulnerability of Server Message Block (SMB). It is confirmed to exploit at least one publicly disclosed SMB vulnerability – CVE 2017-0143 also referred to as “EternalBlue” – which was released by a group called ShadowBrokers in April 2017. Using arbitrary code execution privileges, the ransomware installs itself to the machine, then proceeds to encrypt a wide array of files.
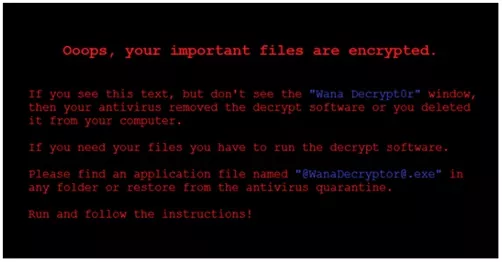
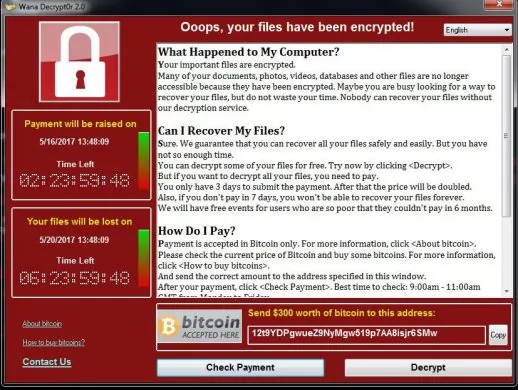
Files are encrypted with the .WNCRY file extension added to them. The ransomware also downloads and installs TOR, with all dependencies, onto the infected machine, and uses this service to reach out to one of at least six .onion domains. The ransomware drops a ransom note named @Please_Read_Me@.txt; it also adds a lock screen, named “WanaCrypt0r 2.0”
At the time of reporting, the malware was requesting $300 USD in BitCoins, though this amount was later increased to $600. The Bitcoin wallets associated with the activity had received approximately 500 ransom payments, estimated to be worth over $150,000.
Additionally, reports indicate the ransomware may have increased its payment demands from $300 to $600, indicating the actors have some level of control over the demanded amount and are increasing the cost of decryption, likely due to the success of the malware.
The ransomware uses a unique encryption key for each binary placed onto a computer, but since the ransomware uses asymmetric RSA encryption even having the encryption key will not allow for convenient decryption.
Upon infection, the following files are created:
%Temp%\b.wnry
%Temp%\c.wnry
%Temp%\m.wnry
%Temp%\r.wnry
%Temp%\t.wnry
%Temp%\u.wnry
%Temp%\m.vbs
%Temp%\taskdl.exe
C:\ProgramData\taskse.exe
%Temp%\[14 random digits].bat
The file c.wry contains information needed by the malware to further the infection and communication with its Command and control server.
13AM4VW2dhxYgXeQepoHkHSQuy6NgaEb94
sqjolphimrr7jqw6[.]onion
https://www.dropbox[.]com/s/deh8s52zazlyy94/t.zip?dl=1
win32-0.2.8.11.zip
https://dist.torproject[.]org/torbrowser/6.5.1/tor-win32-0.2.9.10.zip
https://www.dropbox[.]com/s/c1gn29iy8erh1ks/m.rar?dl=1
Adding the following registry entry for persistence:
HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Run /v “” /t REG_SZ /d
“\”C:\Users\\AppData\Local\Temp\tasksche.exe\”” /f
It also drops the ransom file named @Please_Read_Me@.txt and the decryptor file named @WanaDecryptor@.exe, as shown below:
WannaCrypt0r 2.0 uses TOR hidden services for command and control, dropping and installing a fully functional version of TOR with all necessary components onto an infected machine. The TOR service reaches out to one of a number of .onion domains, including:
- gx7ekbenv2riucmf[.]onion
- 57g7spgrzlojinas[.]onion
- Xxlvbrloxvriy2c5[.]onion
- 76jdd2ir2embyv47[.]onion
- cwwnhwhlz52maqm7[.]onion
- sqjolphimrr7jqw6[.]onion
The following file extensions have been observed affected by this malware:
.der .slk .odb .jsp .3g2 .zip .edb .docm.pfx .wb2 .frm .php .flv .rar .potm .docb.key .odp .myd .asp .wma .tgz .potx .jpg.crt .otp .myi .java .mid .tar .ppam .jpeg.csr .sxd .ibd .jar .m3u .bak .ppsx .snt.p12 .std .mdf .class .m4u .tbk .ppsm .onetoc2.pem .uop .ldf .mp3 .djvu .bz2 .pps .dwg.odt .odg .sln .wav .svg .PAQ .pot .pdf.ott .otg .suo .swf .psd .ARC .ppt m .wk1.sxw .sxm .cpp .fla .nef .aes .xltm .wks.stw .mml .pas .wmv .tiff .gpg .xltx .hwp.uot .lay .asm .mpg .tif .vmx .xlc .rtf.3ds .lay6 .cmd .vob .cgm .vmdk .xlm .csv.max .asc .bat .mpeg .raw .vdi .xlt .txt.3dm .sqlite3 .ps1 .asf .gif .sldm .xlw .vsdx.ods .sqlitedb .vbs .avi .png .sldx .xlsb .vsd.ots .sql .dip .mov .bmp .sti .xlsm .eml.sxc .accdb .dch .m p4 .vcd .sxi .dotx .msg.stc .mdb .sch .3gp .iso .pptx .dotm .ost.dif .dbf .brd .mkv .backup .ppt .dot .pst.xlsx .xls .docx .doc
3. Attack PoC
4. Advisory Notes
The EternalBlue SMB vulnerability was originally published by the Shadow Brokers who allegedly acquired NSA hacking tools. The vulnerability was published in April 2017 but patched prior to release by Microsoft in March 2017. The exploit is particularly dangerous because WannaCry 2.0 a ransomware uses remote code execution vulnerability that does not require any user interaction.
Moreover, the malware can spread laterally as quickly as the commands can be processed by infected machines resulting in the highly virulent nature of this threat. Since the ransomware propagates primarily through the exploitation of the EternalBlue SMB vulnerability, multiple infections in the same organization are to be expected. This is because the exploit leverages a previously-patched Windows vulnerability and if an infected device does not have the appropriate patches it is likely other machines are similarly vulnerable.
The inclusion of over twenty language variants for the ransom note supports the conclusion that this malware was not targeted at a particular country or entity, but rather was intended to spread as widely as possible.
The success of this ransomware attack will almost certainly lead to future ransomware attacks attempting to propagate via critical Microsoft Windows vulnerabilities, even months after the vulnerability is publicly released and patched. The actor(s) behind this activity is currently unknown, and no major group has taken credit for the activity.
5. Mitigation Techniques
Varutra Consulting recommends the following:
- Apply Microsoft patches MS17-010 / MS17-012 disabling SMB v1, and blocking all versions of SMB at the network boundary by blocking TCP port 445 with related protocols on UDP ports 137-138 and TCP port 139 for all boundary devices.
- Due to recent changes in Microsoft patch naming, ensure Microsoft Knowledge Base 4013389 has been applied to all systems, as it is another name for the MS17-010 SMB vulnerability patch.
- Do not pay any ransom associated with this activity. The actors may not even provide a decryption key, and furthermore doing so incentivizes and finances further criminal activity.
- Enable strong spam filters to prevent phishing e-mails from reaching the end users and authenticate in-bound e-mail using technologies like Sender Policy Framework (SPF), Domain Message Authentication Reporting and Conformance (DMARC), and DomainKeys Identified Mail (DKIM) to prevent e-mail spoofing.
- Prevent privileged execution of windows binaries from temp directories.
- Disable macro scripts from Microsoft Office files transmitted via e-mail. Consider using Office Viewer software to open Microsoft Office files transmitted via e-mail instead of full Office suite applications.
- Develop user security awareness training for identifying scams, malicious links, and attempted social engineering.
- Scan your perimeter and other Internet-facing network structures for the presence of open Windows SMB ports.
- Ensure that Snort Signatures ET-2024217, ET-2024218, and ET-2024220 are implemented to ensure lateral propagation detection within an enterprise network and not just at the border or perimeter.
- Below mentioned are the possibly infected IP’s which need to be blocked on firewall immediately.
| 82.94.251.227:443 213.239.216.222:443 51.255.41.65:9001 86.59.21.38:443 198.199.64.217:443 83.169.6.12:9001 192.42.115.102:9004 104.131.84.119:443 178.254.44.135:9001 163.172.25.118:22 197.231.221.221:9001 128.31.0.39:9191
| 149.202.160.69:9001 46.101.166.19:9090 91.121.65.179:9001 2.3.69.209:9001 146.0.32.144:9001 50.7.161.218:9001 217.79.179.177:9001 213.61.66.116:9003 212.47.232.237:9001 81.30.158.223:9001 79.172.193.32:443 38.229.72.16:443 |
Read about Petya Ransomware Threat Advisory blog post here
6. References
https://www.microsoft.com/security/portal/threat/encyclopedia/Entry.aspx?Name=Ransom:Win32/WannaCrypt
https://krebsonsecurity.com/2016/12/before-you-pay-that-ransomware-demand/
http://webcast.gov.in/cert-in/
https://blogs.technet.microsoft.com/msrc/2017/05/12/customer-guidance-for-wannacrypt-attacks/